Welcome to the second edition of the iThemes Security feature spotlight. In these posts, we pick a feature in the iThemes Security Pro plugin and share a bit about why we developed it, who the feature is for, and how to use the feature to strengthen your WordPress website’s security.
Today we are going to cover Trusted Devices, a really cool way to help secure your WordPress site.
Why We Developed Trusted Devices
Let’s say you follow all of the WordPress security best practices to protect your user account. Not only do you use a unique, strong password for every site, but you also lock down all of your online accounts with two-factor authentication. You are a good example of what it looks like to take WordPress security seriously.
Yet, even with all of the security measures you put into place, somehow, your website was still hacked. And, to make matters worse, the attacker used YOUR WordPress user to hack the site. How did this happen to you, the security guru?!
Unfortunately, even if you do everything right to secure your WordPress user account, there are still methods that hackers can use to exploit your account.
For example, WordPress generates a session cookie every time you log into your website. And let’s say that you have a browser extension that has been abandoned by the developer and is no longer releasing security updates. Unfortunately for you, the neglected browser extension has a vulnerability. The vulnerability allows bad actors to hijack your browser cookies, including the earlier-mentioned WordPress session cookie. This type of hack is known as Session Hijacking. So, an attacker can exploit the extension vulnerability to piggyback off your login and start making malicious changes with your WordPress user.
Pretty crummy, right? We agree, so we created a way to protect your account, even when bad actors can find and exploit other vulnerabilities.
What Are Trusted Devices?
The Trusted Devices feature in iThemes Security Pro works to identify the devices that you and other users use to login to your WordPress site. After your devices are identified, we can stop session hijackers and other bad actors from doing any damage on your website.
When a user has logged in on an unrecognized device, Trusted Devices can restrict their administrator-level capabilities. This means that if an attacker were able to break into the backend of your WordPress site, they wouldn’t have the ability to make any malicious changes to your website.
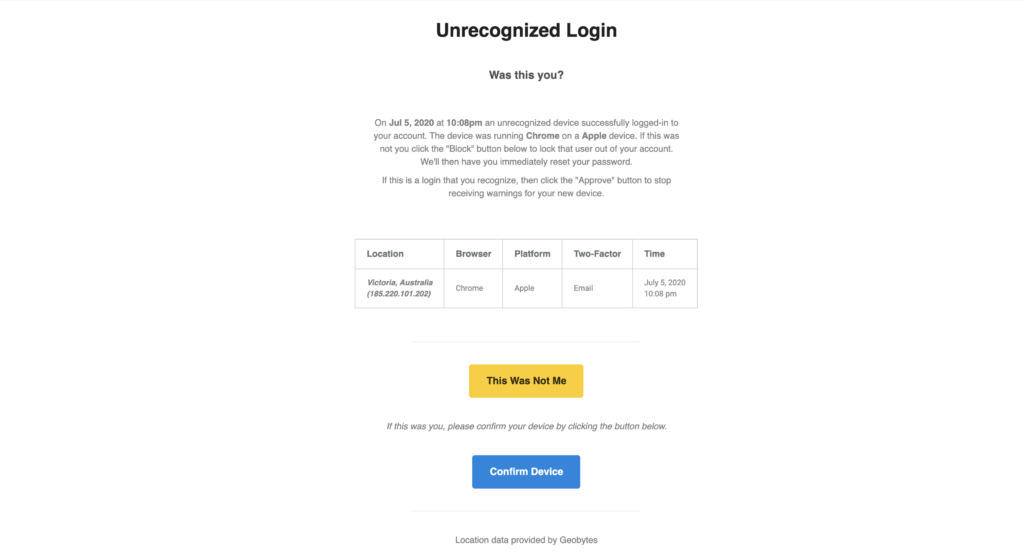
In this scenario, you will receive an email that lets you know that someone logged into your site from an unrecognized device. The email includes an option to block the hacker’s device. Then you can just laugh and laugh, knowing that you ruined a bad guy’s day.
Another benefit of Trusted Devices is that it makes Session Hijacking a thing of the past. If a user’s device changes during a session, iThemes Security will automatically log the user out to prevent any unauthorized activity on the user’s account, such as changing the user’s email address or uploading malicious plugins.
Man, it sure does feel good preventing malicious attacks from being successful!
How to Use the Trusted Devices Feature in iThemes Security Pro
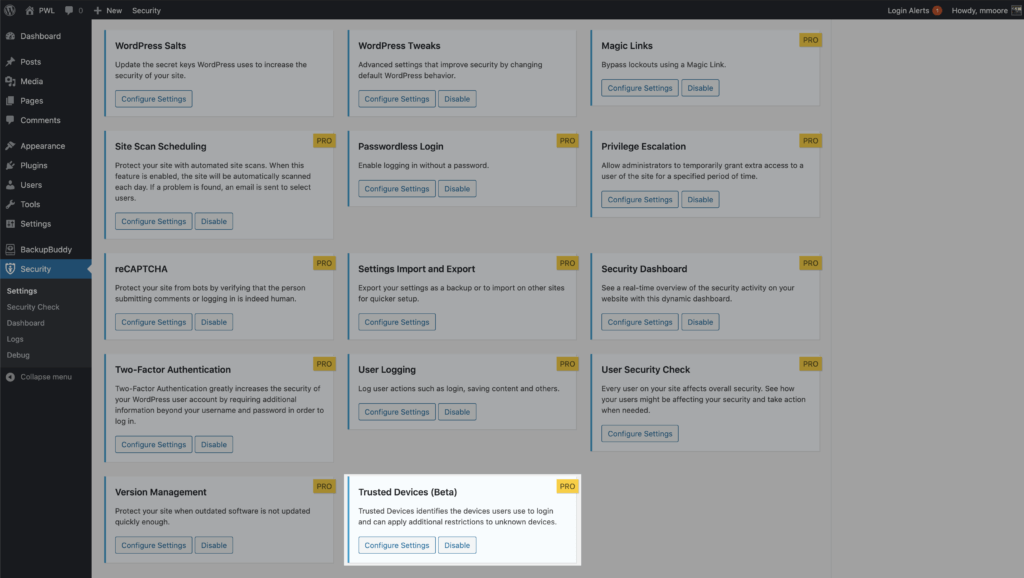
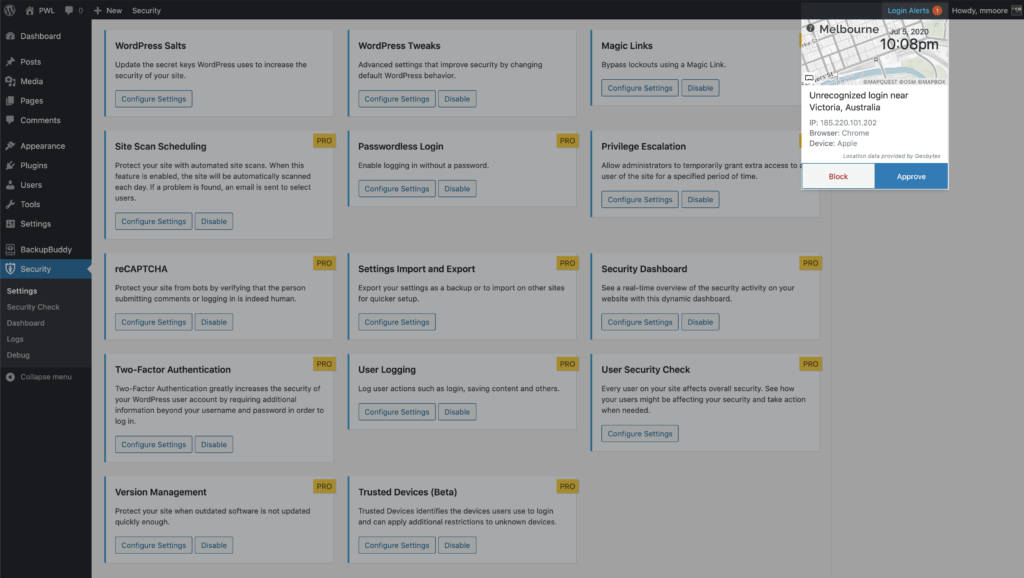
To start using Trusted Devices, enable them on the main page of the security settings, and then click the Configure Settings button.
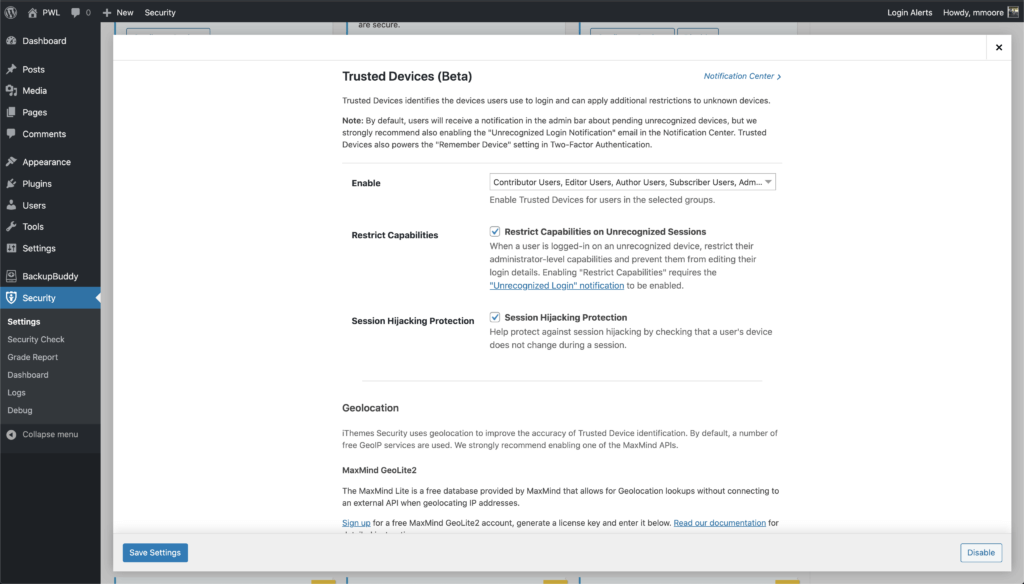
In the Trusted Devices settings, decide which users you want to use the feature, and enable then Restrict Capabilities and Session Hijacking Protection features.
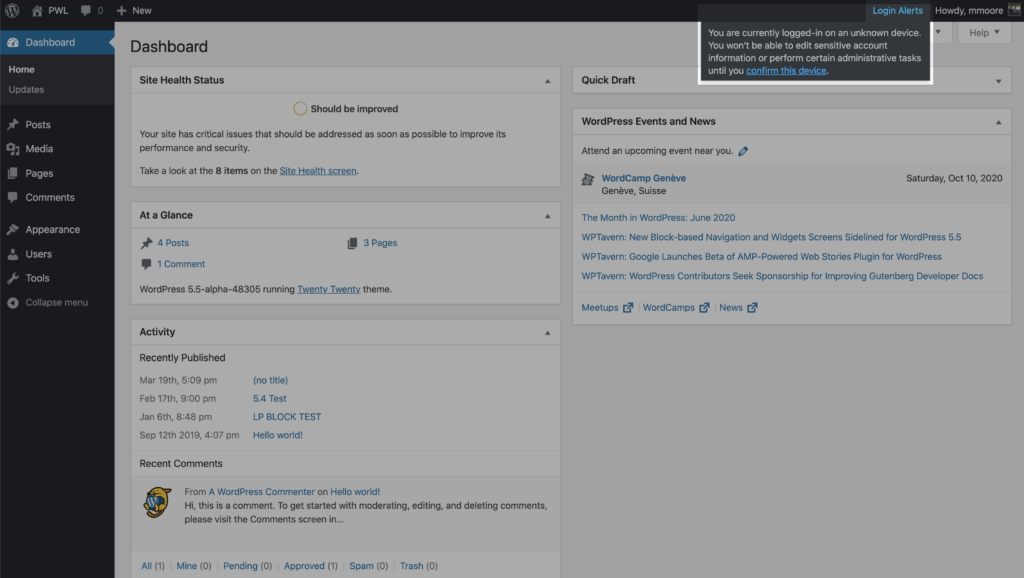
After enabling the new Trusted Devices setting, users will receive a notification in the WordPress admin bar about pending unrecognized devices. If your current device hasn’t been added to the trusted devices list, click the Confirm This Device link to send the authorization email.
Click the Confirm Device button in the Unrecognized Login email to add your current devices to the Trusted Devices list.
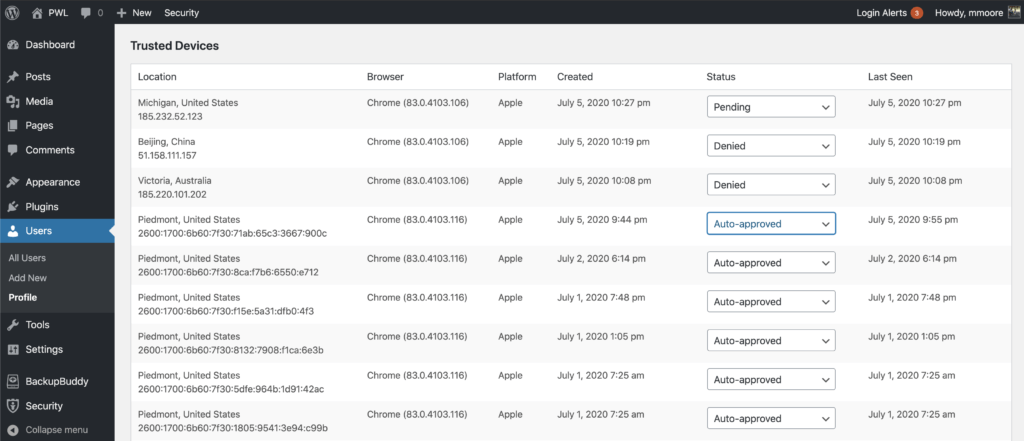
Once Trusted Devices is enabled, users can manage devices from their WordPress User Profile page. From this screen, you can approve or deny devices from the Trusted Devices list.
Additionally, you have the option to signup for some third-part APIs to improve the accuracy of the Trusted Devices identification and to use static image maps to display the approximate location of an unrecognized login. Check out the Trusted Devices setting to see what integrations are available,
Wrapping Up
We didn’t think it was fair for you to do all the work to secure your website, just for some hacker to find a vulnerability loophole. The Trusted Devices feature in iThemes Security Pro allows you to restrict access to your site’s backend to a list of approved devices. Now that is awesome!
Get iThemes Security Pro with Trusted Devices Today
iThemes Security, our WordPress security plugin, gives you over 30+ ways to secure and protect your WordPress site. On average, 30,000 new websites are hacked each day. WordPress sites can be an easy target for attacks because of plugin vulnerabilities, weak passwords and obsolete software.
Most WordPress admins don’t know they’re vulnerable, but iThemes Security works to lock down WordPress, fix common holes, stop automated attacks and strengthen user credentials. With advanced features for experienced users, our WordPress security plugin can help harden WordPress.
Get iThemes Security Pro now
The post iThemes Security Pro Feature Spotlight #2: Trusted Devices appeared first on iThemes.
Source: Security Feed