https://ithemes.com/wordpress-vulnerability-roundup-june-2019-part-2/
New WordPress plugin and theme vulnerabilities were disclosed during the last half of June, so we want to keep you aware.
We divide the WordPress Vulnerability Roundup into four different categories:
- 1. WordPress Core Vulnerabilities
- 2. WordPress Plugin Vulnerabilities
- 3. WordPress Themes Vulnerabilities
- 4. Breaches From Around the Web
*We include breaches from around the web because it is essential to also be aware of vulnerabilities outside of the WordPress ecosystem. Exploits to server software can expose sensitive data. Database breaches can expose the credentials for the users on your site, opening the door for attackers to access your site.
WordPress Core Vulnerabilities
WordPress Plugin Vulnerabilities
Several new WordPress plugin vulnerabilities have been discovered this make. Make sure to follow the suggested action below to update the plugin or completely uninstall it.
1. Messenger Customer Chat
The Messenger Customer Chat plugin, version 1.2, and below, is vulnerable to a Cross-Site Request Forgery attack. The vulnerability will allow an attacker to change some of the WordPress site settings.
What You Should Do
2. Support Board – Chat And Help Desk | Support & Chat
The Support Board – Chat And Help Desk | Support & Chat plugin, version 1.2.8, and below, is vulnerable to a Cross-Site Scripting attack.
What You Should Do
3. Seo by Rank Math

The Seo by Rank Math plugin, version 1.0.26, and below, is vulnerable to a Cross-Site Scripting attack.
What You Should Do
4. WP-Members Membership Plugin
The WP-Members Membership plugin, version 3.2.7, and below, is vulnerable to a Cross-Site Request Forgery attack. The vulnerability will allow an attacker to create, edit, and delete new fields.
What You Should Do
5. Real Estate Manager

The Real Estate Manager plugin is vulnerable to a Plugin Arbitrary Settings Update attack. The lack of authorization and CSRF checks in the save_admin_settings() AJAX function is the cause of the vulnerability.
What You Should Do
6. LionScripts: IP Blocker Lite

The LionScripts: IP Blocker Lite plugin, version 10.3, and below, is vulnerable to a Cross-Site Request Forgery attack that could lead to an Arbitrary File Upload attacks.
What You Should Do
7. WebP Express

The WebP Express plugin, version 0.14.10, and below, are vulnerable to a multitude of attacks, Cross-Site Request Forgery, Arbitrary File Upload, Cross-Site Scripting, an Unauthorized Access attacks.
What You Should Do
8. Import users from CSV with meta
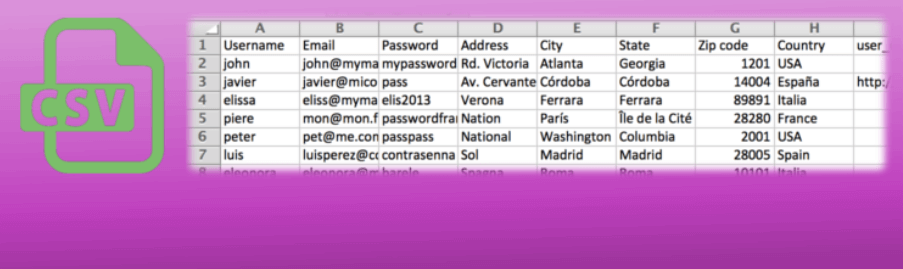
The Import users from CSV with meta plugin, version 1.14.1.2, and below, is vulnerable to a Cross-Site Scripting attack.
What You Should Do
9. Deny All Firewall
The Deny All Firewall plugin, version 1.14.1.2, and below, is vulnerable to a Cross-Site Request Forgery attack. The vulnerability would allow an attacker to remove the Deny All Firewall from the .htaccess and render the plugin useless.
What You Should Do
10. Facebook for WooCommerce
The Facebook for WooCommerce plugin, version 1.9.12, and below, is vulnerable to a Cross-Site Request Forgery attack.
The vulnerability will allow an attacker to change some of the WordPress site settings.
What You Should Do
11. Shortlinks by Pretty Links – Best WordPress Link Tracking Plugin

The Shortlinks by Pretty Links plugin, version 2.1.9, and below, is vulnerable to a Cross-Site Scripting and a CSV Injection attack. The vulnerability would allow an attacker to inject malicious code in the WordPress dashboard.
The vulnerability will allow an attacker to change some of the WordPress site settings.
What You Should Do
12. Sina Extension for Elementor
The Sina Extension for Elementor plugin, version 2.1.9, and below, is vulnerable to a Local File Inclusion attack.
What You Should Do
13. CP Contact Form with PayPal
The CP Contact Form with PayPal plugin, version 1.3.01, and below, is vulnerable to a Cross-Site Scripting attack.
What You Should Do
14. Share This Image
The Share This Image plugin, version 1.19, and below, is vulnerable to a Cross-Site Scripting attack.
What You Should Do
15. ads-for-wp
The ads-for-wp plugin is vulnerable to a Cross-Site Request Forgery attack.
What You Should Do
16. User Email Verification for WooCommerce
The User Email Verification for WooCommerce plugin, version 3.3.0, and below, is vulnerable to a Cross-Site Request Forgery attack leading to an Option update.
What You Should Do
17. Advanced Woo Search
The Advanced Woo Search plugin, version 1.6.8, and below, is vulnerable to a Cross-Site Request Forgery leading to a Cross-Site Scripting attack.
What You Should Do
18. ACF: Better Search

The ACF: Better Search plugin, version 3.3.0, and below, is vulnerable to a Cross-Site Request Forgery attack.
What You Should Do
19. Widget Logic

The Widget Logic plugin, version 5.9.0, and below, is vulnerable to a Cross-Site Request Forgery leading to a Remote Code Execution attack.
Danne Witz reported that attackers could make admin users add malicious code to custom sidebar widgets resulting in remote code execution.
What You Should Do
WordPress Theme Vulnerabilities
How to Be Proactive About WordPress Theme & Plugin Vulnerabilities
Running outdated software is the number one reason WordPress sites are hacked. It is crucial to the security of your WordPress site that you have an update routine. You should be logging into your sites at least once a week to perform updates.
Automatic Updates
Using the iThemes Security Pro plugin’s Version Management feature, you can enable automatic WordPress updates to ensure you are getting the latest security patches.
Automatic updates are an excellent choice for websites that don’t change very often. The lack of needed attention usually leaves these sites neglected and vulnerable to attacks.
Version Management Updates
- WordPress Automatic Updates – All WordPress updates are automatically installed when available.
- Plugin Automatic Updates – All plugin updates are automatically installed when available.
- Theme Automatic Updates – All theme updates are automatically installed when available. Use this if you’ve put your theme customizations in a child theme, to not override your customizations by updating the parent theme.
- Granular Control over Plugin and Theme updates – You may have plugins/themes that you’d like to either manually update, or delay the update until the release has had time to prove stable. You can choose Custom for the opportunity to assign each plugin or theme to either update immediately (Enable), not update automatically at all (Disable) or update with a delay of a specified amount of days (Delay).
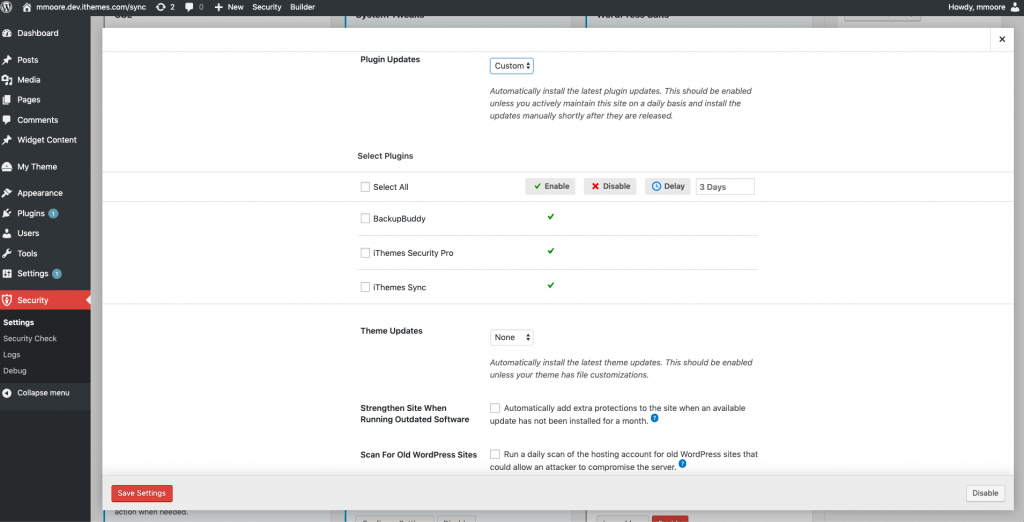
Strengthening and Alerting to Critical Issues
- Strengthen Site When Running Outdated Software – The iThemes Security plugin will automatically enable stricter security when an update has not been installed for a month. First, it will force all users that do not have two-factor enabled to provide a login code sent to their email address before logging back in. Second, it will disable the WP File Editor (to block people from editing plugin or theme code), XML-RPC pingbacks and block multiple authentication attempts per XML-RPC request (both of which will make XML-RPC stronger against attacks without having to turn it off completely).
- Scan for Other Old WordPress Sites – This will checks for other outdated WordPress installs on your hosting account. A single outdated WordPress site with a vulnerability could allow attackers to compromise all the other sites on the same hosting account.
- Send Email Notifications – For issues that require intervention, an email is sent to admin-level users.
Breaches From Around the Web
1. Kubernetes Command Line Interface Flaw
Kubectl is a command line interface for Kubernetes–the open source container managed created by Google– has a pretty ugly vulnerability. The kubectl cp command could enable a directory traversal so that a malicious container could replace or create files on a users workstation.
Be sure you update kubectl to a version that has been patched.
2. NASA Gets Hacked

An unauthorized Raspberry Pi device that was connected to the Jet Propulsion Laboratory servers was compromised. After successfully attacking the Raspberry Pi device the hackers were able to gain access to other systems, including the Deep Space Network array of radio telescopes.
The story highlights the importance of security every device on your network.
3. Netflix Finds Linux and FreeBSD Vulnerabilities
Netflix’s streaming service requires a huge infrastructure, powerful tools, and talented people. You can watch Branden Gregg live debugging Minecraft or check out the Netflix open source software center to see that Netflix is as much of a tech company as it is an entertainment company.
Now that you know Netflix is a tech company, it shouldn’t be a surprise that they discovered and disclosed three vulnerabilities. The two Linux and one FreeBSD are all TCP based denial of service attacks. You can find a detailed explanation of the vulnerabilities and workarounds on Netflix’s GitHub.
A WordPress Security Plugin Can Help Secure Your Website
iThemes Security Pro, our WordPress security plugin, offers 30+ ways to secure and protect your website from common WordPress security vulnerabilities. With WordPress two-factor authentication, brute force protection, strong password enforcement, and more, you can add an extra layer of security to your website.
Get iThemes Security Pro
The post WordPress Vulnerability Roundup: June 2019, Part 2 appeared first on iThemes.
Source: Security Feed