Podcast Episode 47: Staying Secure through Community Cooperation with GiveWP’s Matt Cromwell
Podcast Episode 47: Staying Secure through Community Cooperation with GiveWP’s Matt Cromwell At WordCamp Sacramento, Matt Cromwell from GiveWP talked with us about how Give began, their mission of democratizing generosity, and how they handled the vulnerability...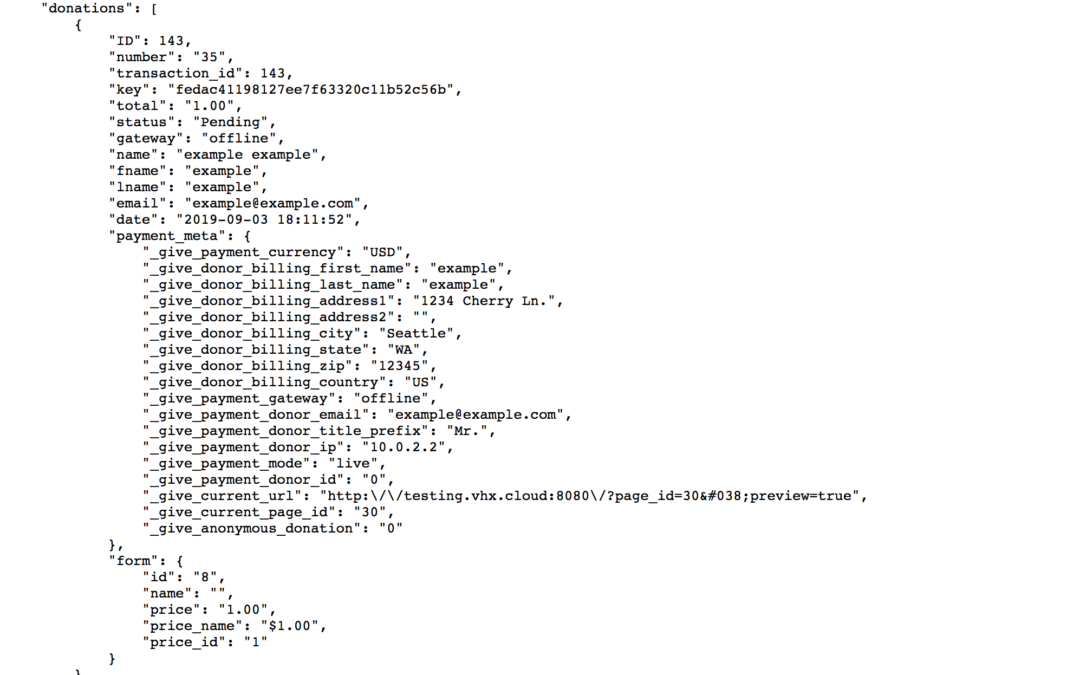
Authentication Bypass Vulnerability in GiveWP Plugin
Authentication Bypass Vulnerability in GiveWP Plugin Description: Authentication Bypass with Information DisclosureCVSS v3.0 Score: 7.5 (High)CVSS Vector String: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:NAffected Plugin: GiveWPPlugin Slug: giveAffected...Podcast Episode 46: Zero Day Vulnerability in Rich Reviews Plugin Exploited In The Wild
Podcast Episode 46: Zero Day Vulnerability in Rich Reviews Plugin Exploited In The Wild We chat with Mikey Veenstra to talk about the Wordfence Threat Intelligence team’s work tracking a series of active attacks on an unpatched vulnerability in the Rich Reviews...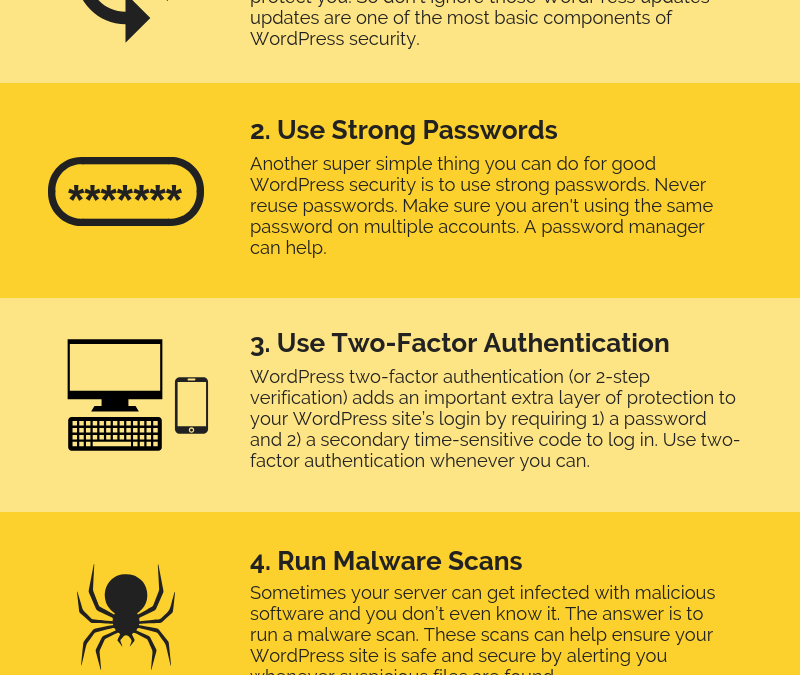
8 WordPress Security Infographics to Download & Share
https://ithemes.com/wordpress-security-infographics/Love infographics? We do, too! From WordPress security basics to how to secure your website, we have 8 WordPress security infographics for you to download and share. 1. Five Ways to Secure Your WordPress Website It...
Zero-Day RCE in vBulletin v5.0.0-v5.5.4
http://feedproxy.google.com/~r/sucuri/blog/~3/C0lXQcD0tyc/zero-day-rce-in-vbulletin-v5-0-0-v5-5-4.html A new remote code execution (RCE) zero-day vulnerability has been disclosed by an anonymous researcher on the Full Disclosure mailing list this past Monday....
Stop WordPress from Changing .htaccess
https://perishablepress.com/stop-wordpress-changing-htaccess/ In a recent tutorial, I explain how to Stop WordPress from modifying .htaccess. That post explains several ways to prevent WordPress from making changes to .htaccess. This post explains an even better way...DELUCKS SEO <= 2.1.7 – Unauthenticated Options Update
https://wpvulndb.com/vulnerabilities/9886 Source: Security FeedRich Reviews <= 1.7.4 – Unauthenticated Plugin Options Update
https://wpvulndb.com/vulnerabilities/9885 Source: Security Feed